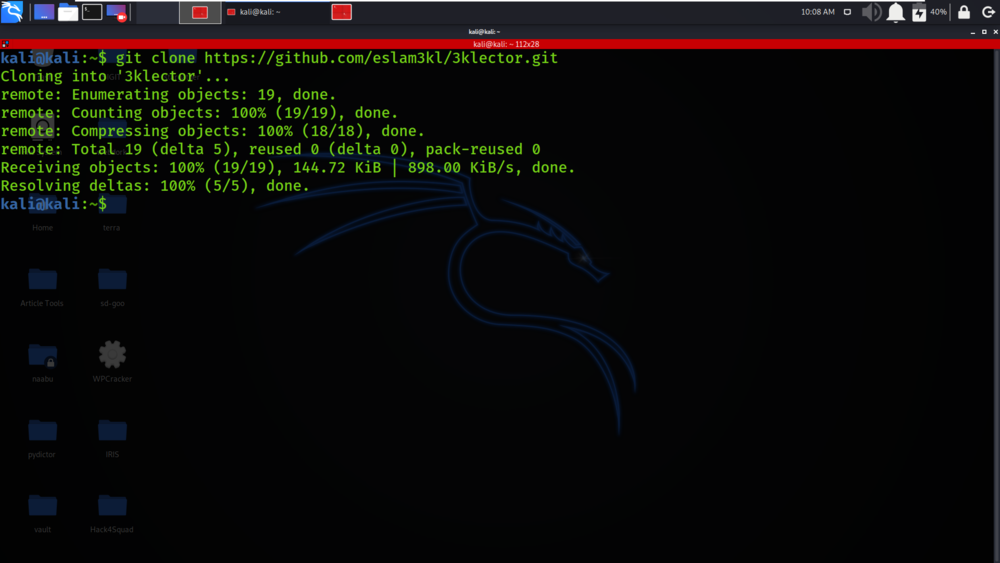
BigBountyRecon - Utilises 58 Different Techniques On Intial Reconnaissance On The Target Organisation

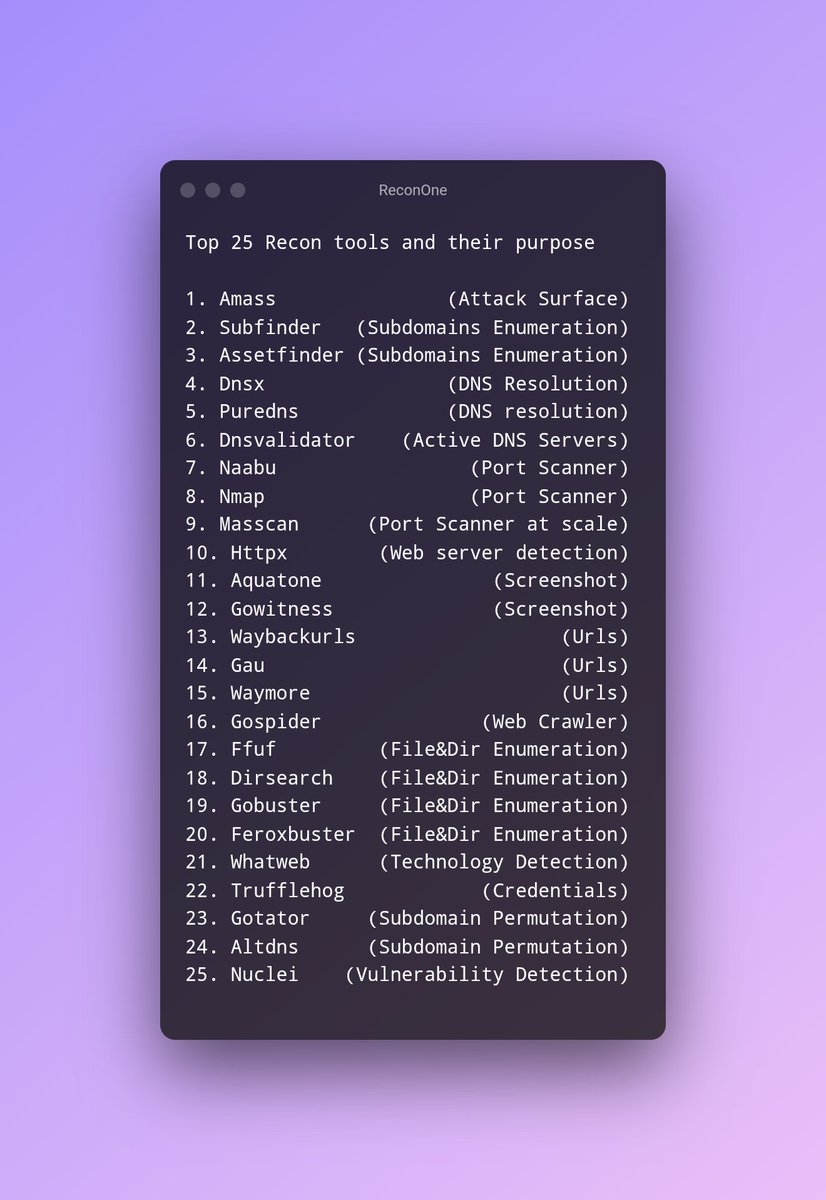
Daily Dark Web on X: "Top 25 Recon Tools #cybersecurity #infosec #recon https://t.co/6wpYMugY3r" / X

Comparison of some of the most relevant tools for shortening the Recon... | Download Scientific Diagram